Table of Contents
- Introduction: The Ghost in the Machine
- Field Challenges: The Tangled Web of Legacy Systems
- The Cyberdeck Solution: A Modular Intelligence Platform
- Component Analysis: Building Your Tactical Toolkit
- Software Stack: Orchestrating the Data Flow
- Operational Advantages: Why Modularity Wins
- Building Your Own Custom Cyberdeck: A Blueprint for Operators
- Engineer's Verdict: Is the Custom Cyberdeck Worth the Deployment?
- Operator's Arsenal: Essential Gear for Satellite Ops
- Frequently Asked Questions
- The Contract: Your First Field Operation Scenario
The static crackled on the comms, a phantom whisper in the vast expanse of the signal spectrum. For too long, satellite and radio astronomy operators have been shackled by a tangled mess of wires and disparate devices, a Frankenstein's monster of equipment that balks at deployment. It’s a familiar story in the trenches – efficiency sacrificed at the altar of convenience. But in this digital wilderness, innovation is not a luxury, it's a survival instinct. One operator, driven to the brink by cable clutter, engineered a radical solution: a custom cyberdeck, meticulously crafted for the clandestine world of satellite intelligence and radio astronomy.

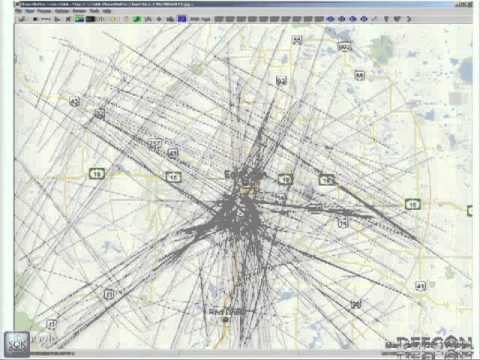
Operating in the field, especially when dealing with the subtle nuances of satellite communications and radio astronomy, presents a unique set of logistical nightmares. The complexity of the required hardware often forces experimenters into a precarious dance with multiple devices, each with its own power source, cabling, and software dependencies. This fragmentation turns a potential intelligence-gathering mission into a chaotic exercise in cable management and system configuration. The risk of misconfiguration or failure increases exponentially, turning valuable field time into a frustrating battle against your own setup.
This isn't just a box; it's an all-in-one command center. The custom cyberdeck consolidates the critical elements of satellite operations and radio astronomy into a single, portable platform. Think of it as your mobile SIGINT station, streamlined and optimized for rapid deployment. It integrates essential hardware like a touchscreen computer, the ubiquitous RTL-SDR radio, specialized filter and amplifier modules, robust WiFi connectivity, a satellite meter doubling as a digital video player, and even PTZ controls for legacy dish pointers. The inclusion of an LNB power injector and easily accessible panel-mount port interfaces ensures seamless connectivity and power management in any environment. This is about consolidating function and maximizing operational tempo.
Component Analysis: Building Your Tactical Toolkit
At its core, this cyberdeck is a testament to modular design, a principle that should be gospel for any field operator. The major components are not permanently affixed but rather secured with industrial-strength velcro tape. This isn't just for aesthetics; it's a tactical advantage allowing for swift replacement or reconfiguration of modules based on the mission profile. Need enhanced filtering for a specific frequency band? Swap it in. Experimenting with different antenna gain characteristics? The modules are designed for rapid interchangeability. This flexibility is crucial when operating under pressure and in unpredictable conditions.
Key hardware components typically include:
- Touchscreen Computer: The central console for all operations. Low-resource demands are paramount.
- RTL-SDR Radio: The workhorse for capturing raw signal data. Versatile and cost-effective.
- Filter/Amp Modules: Tailored signal conditioning is essential for clean data acquisition.
- WiFi Modules: For network connectivity, remote access, or data exfiltration.
- Satellite Meter/DVDP: Essential for signal strength assessment and video stream analysis.
- PTZ Controls: For precise directional adjustments of older dish systems.
- LNB Power Injector: Crucial for powering satellite receivers.
- Panel-Mount Port Interfaces: Streamlining external connections.
Software Stack: Orchestrating the Data Flow
Hardware is only half the equation. The intelligence gleaned from satellite operations hinges on a robust and efficient software stack. This cyberdeck employs a carefully selected suite of tools, prioritized for low resource consumption and high functionality:
- Q4OS: A lightweight, resource-efficient Linux distribution that provides a stable foundation without bogging down the system.
- GQRX: The de facto standard for Software Defined Radio (SDR) operation, offering real-time signal visualization and analysis.
- Gpredict: Essential for satellite tracking, providing orbital data and predicting passes, which is critical for timing data collection windows.
- GOEStools: Specifically for processing NOAA satellite imagery.
- WXtoIMG: Another powerful tool for decoding and processing weather satellite data.
- And others: Depending on the specific mission, specialized tools for signal analysis, data logging, or communication protocols may be integrated.
The synergy between this hardware and software configuration enables a single operator to manage complex satellite and radio astronomy experiments from a unified interface, transforming potential chaos into controlled intelligence gathering.
Operational Advantages: Why Modularity Wins
The benefits of a custom-built cyberdeck for satellite and radio astronomy operations are manifold, directly impacting an operator's effectiveness and efficiency in the field. It's not merely about having the gear; it's about having the *right* gear, configured for the mission, and accessible when minutes count.
- Single-Point Operation: All necessary equipment is consolidated into one portable platform. This drastically reduces setup time and minimizes the logistical burden of transporting and managing multiple disparate devices. Field operations become more agile and less prone to equipment failure due to tangled or improperly connected wires.
- Enhanced Modularity and Expandability: The velcro-based modular system allows for rapid swapping of components. This adaptability is invaluable for experimenters who may need to pivot their focus or adapt to unexpected signal conditions. If a specific filter isn't performing optimally, or a new sensor needs to be integrated, the process is logistically simple and quick.
- Unified Control Interface: Operating all equipment from a single interface simplifies complex experiments. Coordinating efforts, monitoring signal integrity, and collecting data become streamlined tasks, allowing the operator to focus on the analysis and interpretation of the gathered intelligence rather than wrestling with the machinery.
This consolidation of function transforms the operator from a technician juggling devices into an analyst leveraging a unified intelligence platform.
Building Your Own Custom Cyberdeck: A Blueprint for Operators
Embarking on the construction of your own custom cyberdeck requires a methodical, operator-centric approach. This isn't a hobbyist project; it's a tactical build. The process demands a clear understanding of your operational objectives.
- Define Mission Parameters: Before touching any hardware, meticulously determine the specific components and functionalities required for your intended experiments. What frequencies will you target? What data do you need to acquire? What level of signal processing is necessary? This dictates your component selection.
- Select a Resource-Efficient Operating System: Choose an OS that can handle your chosen software without becoming a bottleneck. Lightweight Linux distributions like Q4OS, Bodhi Linux, or even a carefully configured Raspberry Pi OS are prime candidates. Stability and low overhead are paramount.
- Prioritize a Modular Platform: Opt for a chassis or enclosure that facilitates easy component integration and removal. The velcro tape method is a practical, low-cost solution, but consider more robust mounting systems if durability under extreme conditions is a concern.
- Component Sourcing and Integration: Gather your selected components. When assembling, pay close attention to power requirements and signal integrity. Ensure all connections are secure and clearly labeled. Proper labeling of modules and cables is non-negotiable for rapid troubleshooting in the field.
Remember, the goal is not just to assemble a collection of parts, but to engineer a cohesive, reliable intelligence-gathering platform.
Engineer's Verdict: Is the Custom Cyberdeck Worth the Deployment?
The custom cyberdeck, particularly when tailored for specialized tasks like satellite and radio astronomy operations, represents a significant leap in field efficiency. For organizations or individuals who frequently engage in such activities, the advantages of a self-contained, modular platform are undeniable. It moves beyond the limitations of off-the-shelf solutions, offering a bespoke environment optimized for specific intelligence-gathering needs. While the initial investment in time and components might seem substantial, the long-term gains in operational tempo, data quality, and mission flexibility often outweigh the costs. It’s a strategic deployment of resources, transforming a chaotic setup into a potent, single-interface intelligence tool.
Operator's Arsenal: Essential Gear for Satellite Ops
To equip yourself for the challenges of satellite intelligence and radio astronomy, a curated set of tools is essential. Beyond the custom cyberdeck itself, consider these complementary pieces of gear:
- High-Gain Antennas: Depending on your target satellites and frequencies, specialized directional antennas are critical for capturing weak signals.
- Portable Power Solutions: Reliable power is non-negotiable. Consider high-capacity power banks, solar chargers, or even small, quiet generators for extended field operations.
- Signal Analyzers: While the SDR is powerful, dedicated hardware signal analyzers can offer deeper insights into signal characteristics.
- Robust Laptop/Tablet: A secondary, mission-critical device that can withstand environmental conditions and offer computational backup.
- Secure Communication Devices: Encrypted radios or satellite phones for command and control are vital for maintaining operational security.
- Field Tools: Basic toolkit, crimping tools, cable testers, and multimeters are indispensable for on-the-fly repairs and troubleshooting.
- Relevant Literature: Essential reading includes "The ARRL Satellite Communications Manual" for amateur radio satellite operations, and for more general signal intelligence, "The Pragmatic Programmer" offers timeless advice on software engineering best practices applicable to any complex system.
- Certifications: While not 'gear' in the physical sense, demonstrating expertise in SDR, network security, or specific satellite communication protocols (e.g., through courses offered by leading cybersecurity training providers) bolsters operational credibility.
Frequently Asked Questions
- What is the primary advantage of using a custom cyberdeck over standard equipment?
- The primary advantage is integration and modularity. It consolidates disparate components into a single, portable unit, drastically reducing setup time and complexity in the field, while allowing for quick adaptation to different experimental needs.
- Is building a cyberdeck expensive?
- The cost can vary significantly based on the components chosen. An RTL-SDR-based system can be relatively inexpensive, while high-end computing and specialized radio hardware can increase the price considerably. The key is to tailor the build to your specific requirements to manage costs effectively.
- What are the legal considerations for satellite hacking?
- Accessing or interfering with satellite communications without authorization is illegal and carries severe penalties. This guide focuses on legal applications such as amateur radio satellite tracking, weather satellite data reception, and radio astronomy research, all of which operate within legal frameworks.
- How difficult is it to assemble?
- Assembly difficulty depends on your technical proficiency and the complexity of the chosen components. For a basic setup, it can be straightforward, especially with modular designs. More advanced configurations may require soldering and deeper knowledge of electronics and software integration.
The Contract: Your First Field Operation Scenario
Imagine you've deployed your custom cyberdeck to a remote location. Your objective: to capture clear imagery from a specific weather satellite during its next pass. The satellite is scheduled to be visible in 45 minutes. Your cyberdeck is configured with Q4OS, GQRX, and WXtoIMG. Your task:
- Establish a stable power source for your cyberdeck.
- Using Gpredict, accurately determine the satellite's elevation and azimuth at your location for the upcoming pass.
- Configure GQRX to tune to the correct frequency for the satellite's downlink, applying any necessary filters to reduce noise from terrestrial interference.
- Ensure WXtoIMG is ready to receive and process the raw data stream from GQRX.
- Precisely point your antenna using the PTZ controls (if applicable, or manually) to track the satellite during its pass.
- Record the entire pass and process the data with WXtoIMG to generate clear weather images.
Document any challenges encountered during setup or data acquisition. What adjustments would you make for the next mission?