STRATEGY INDEX
- 1. The Genesis of Kingpin
- 2. Fueling the Passion: Hacking, Technology, and Engineering
- 3. Inside the Mind of a Hardware Hacker
- 4. The Ecosystem of Innovation: Altium and Beyond
- 5. Comparative Analysis: Hardware Hacking vs. Software Exploitation
- 6. The Engineer's Verdict on Joe Grand's Legacy
- 7. Frequently Asked Questions
- 8. About the Author
- 9. Mission Debrief: Your Next Steps
1. The Genesis of Kingpin
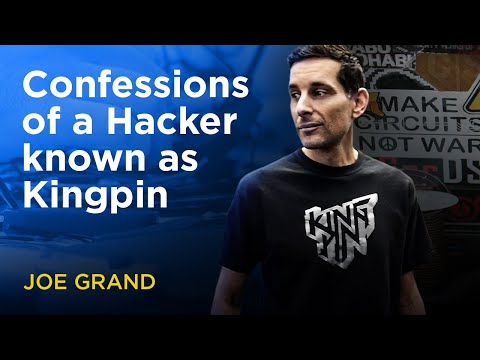
In the annals of digital exploration, few names resonate with the raw, hands-on ingenuity as that of Joe Grand. Known in the clandestine circles of hardware manipulation as "Kingpin," Grand’s journey is not merely a story of technical prowess, but a testament to an insatiable curiosity that has been dismantling and understanding electronic devices since the vibrant, experimental era of the 1980s. This dossier delves deep into the life, motivations, and the very essence of being a hardware hacker, offering a rare glimpse into the mind that sees beyond the surface of circuits and code.
Our objective is to dissect the foundational elements that forged Kingpin, understanding how a childhood fascination evolved into a career defined by reverse engineering, creative problem-solving, and an unwavering passion for the intricate dance of electricity and engineering. This is more than a biography; it's an operational blueprint for understanding the mindset of a master.
2. Fueling the Passion: Hacking, Technology, and Engineering
The fire that ignites a true hacker is often a blend of relentless curiosity and the sheer joy of understanding how things work – and how they can be made to work differently. For Joe Grand, this was evident from an early age. His exploration began not with complex algorithms or network protocols, but with the tangible world of hardware. The 1980s, a burgeoning age of personal computers and accessible electronics, provided fertile ground for a young mind eager to probe the internals of these new machines.
This deep-seated drive to manipulate electronic devices is the core of his identity as "Kingpin." It's about more than just breaking things; it's about understanding their fundamental architecture, their limitations, and their potential. This passion is fueled by a symbiotic relationship between hacking, technology, and engineering:
- Hacking as a Catalyst: The act of hacking, in its purest form, is problem-solving under constraint. It pushes the boundaries of what's possible, often leading to discoveries that even the original designers never envisioned. For Grand, this meant taking apart radios, modifying game consoles, and understanding the flow of signals.
- Technology as the Medium: The ever-evolving landscape of technology provides the raw material. From early microprocessors to complex modern System-on-Chips (SoCs), each iteration presents new challenges and opportunities for exploration.
- Engineering as the Foundation: A profound understanding of electrical engineering principles – circuit design, signal integrity, power management, and digital logic – is the bedrock upon which hardware hacking is built. It allows for informed manipulation and prediction of device behavior.
This intersection is where Grand thrives, transforming abstract concepts into tangible realities through meticulously crafted interventions in the physical world of electronics.
3. Inside the Mind of a Hardware Hacker
What distinguishes a hardware hacker like Joe Grand? It's a mindset characterized by a unique blend of analytical rigor, creative intuition, and an almost obsessive attention to detail. While software hackers navigate the abstract realm of code, hardware hackers operate in the physical world, wielding oscilloscopes, logic analyzers, and soldering irons as their primary tools.
Grand's approach embodies several key traits:
- Deep Curiosity: An unending desire to understand the "why" and "how" behind every component and connection. This isn't satisfied by superficial knowledge; it demands a granular understanding.
- Systematic Deconstruction: The ability to break down complex systems into their constituent parts, analyze each element, and understand their interdependencies. This often involves meticulous documentation and diagramming.
- Resourcefulness: Making do with available tools, even if unconventional. This can mean repurposing equipment, creating custom jigs, or developing novel techniques to extract information or bypass security measures.
- Patience and Persistence: Hardware hacking is rarely a quick process. It demands hours, days, or even weeks of patient investigation, trial and error, and meticulous debugging. Failures are not endpoints but valuable data points.
- Ethical Framework: While the term "hacker" can carry negative connotations, individuals like Grand operate within a strong ethical framework, focusing on understanding, education, and responsible disclosure.
This mental architecture allows "Kingpin" to not only understand the intricate workings of electronic devices but to creatively repurpose, analyze, and sometimes, even reveal hidden functionalities or vulnerabilities within them. It's a lifestyle defined by constant learning and the pursuit of knowledge in the physical digital domain.
4. The Ecosystem of Innovation: Altium and Beyond
The journey of a hardware hacker like Joe Grand doesn't exist in a vacuum. It thrives within a broader ecosystem of technological advancement and innovation. Platforms that foster learning, sharing, and the development of new tools are crucial. The Altium Stories channel serves as a prime example of such an initiative, dedicated to showcasing the cutting edge of electronics and the brilliant minds behind it.
Altium LLC plays a pivotal role in accelerating this innovation. Their software empowers a vast community of engineers and designers, from burgeoning inventors to established global corporations, to bring their electronic ideas to life. By providing sophisticated yet accessible tools for PCB design and realization, Altium democratizes the process of hardware creation, allowing more individuals to engage with the very systems that hackers like Kingpin explore and understand.
Key Takeaways from the Altium Ecosystem:
- Democratization of Design: Advanced software makes complex PCB design achievable for a wider audience.
- Accelerated Innovation Cycles: Efficient tools reduce time-to-market for new electronic products.
- Community and Knowledge Sharing: Platforms like Altium Stories foster collaboration and learning within the engineering and design community.
Understanding this broader context highlights how the foundational work of hardware hackers like Joe Grand informs and inspires the very industry that builds the future of electronics.
5. Comparative Analysis: Hardware Hacking vs. Software Exploitation
While both hardware and software hacking fall under the broad umbrella of cybersecurity and reverse engineering, they represent distinct disciplines with different methodologies, tools, and challenges. Understanding these differences provides a more nuanced appreciation for the unique skills exemplified by Joe Grand.
Hardware Hacking:
- Focus: Physical components, circuits, firmware, embedded systems, signal analysis.
- Tools: Oscilloscopes, logic analyzers, multimeters, soldering irons, JTAG/SWD debuggers, signal generators, microscopes, specialized firmware dumping tools.
- Methodology: Involves physical interaction, de-soldering, signal probing, firmware extraction, and analysis of electrical characteristics. Often requires deep knowledge of electronics manufacturing and component datasheets.
- Challenges: Physical access, component-level security (e.g., secure bootloaders, encryption), specialized equipment costs, environmental factors.
- Examples: Extracting firmware from a microcontroller, bypassing hardware security features, analyzing communication protocols via signal interception, modifying IoT devices.
Software Exploitation:
- Focus: Code, operating systems, network protocols, application vulnerabilities, memory corruption.
- Tools: Debuggers (GDB, WinDbg), disassemblers/decompilers (IDA Pro, Ghidra), network sniffers (Wireshark), fuzzers, exploit frameworks (Metasploit).
- Methodology: Involves static and dynamic code analysis, reverse engineering binaries, identifying logic flaws, crafting malicious inputs, and understanding memory management.
- Challenges: Obfuscation, anti-debugging techniques, complex software architectures, diverse operating systems and platforms.
- Examples: Finding buffer overflows, SQL injection vulnerabilities, cross-site scripting (XSS) flaws, developing malware, analyzing network traffic for sensitive data.
Key Differences:
- Tangibility: Hardware hacking is grounded in the physical world; software hacking is abstract.
- Barrier to Entry: Initial hardware hacking can sometimes have a lower barrier to entry (e.g., modifying simple circuits), but deep expertise is demanding. Software exploitation often requires strong programming and systems knowledge from the outset.
- Scope: Hardware vulnerabilities can sometimes provide a fundamental "root" access that bypasses software security, while software exploits target the logic and implementation of code.
Joe Grand's expertise as "Kingpin" lies firmly in the hardware domain, demonstrating a mastery of understanding and manipulating the physical underpinnings of technology. This perspective provides a crucial layer of security analysis that complements traditional software security efforts.
6. The Engineer's Verdict on Joe Grand's Legacy
From an engineering standpoint, Joe Grand's contributions as "Kingpin" are invaluable. His decades-long dedication to dissecting, understanding, and innovating within the realm of hardware hacking exemplify the core principles of engineering: analysis, design, implementation, and rigorous testing. Grand doesn't just explore vulnerabilities; he embodies the spirit of deep technical investigation that is essential for building more robust and secure systems.
His work serves as a critical feedback loop for the entire technology industry. By revealing how devices can be manipulated, he implicitly provides blueprints for their defense. His passion for technology and engineering is not just a personal pursuit; it's a vital service that pushes the boundaries of what we understand about the electronic world around us.
The "Kingpin" moniker is more than a handle; it signifies a master of his craft, someone who commands an intricate understanding of electronic systems. His legacy is one of profound technical insight, relentless curiosity, and a commitment to pushing the envelope of what's possible in hardware security and engineering.
7. Frequently Asked Questions
Q1: What exactly is hardware hacking?
A1: Hardware hacking involves modifying or manipulating the physical components of electronic devices to alter their functionality, bypass security features, or extract information. It's about interacting directly with the circuitry and firmware.
Q2: Is hardware hacking illegal?
A2: The legality depends heavily on intent and ownership. Modifying devices you own for personal understanding or improvement is generally legal. However, tampering with devices you do not own, or using hardware hacking for malicious purposes like theft or unauthorized access, is illegal and carries severe penalties.
Q3: What are the essential tools for a beginner hardware hacker?
A3: For beginners, essential tools include a reliable soldering iron and solder, a multimeter for basic electrical measurements, a set of precision screwdrivers, basic jumper wires, and potentially a USB-to-serial adapter or a logic analyzer for examining data lines.
Q4: How does hardware hacking differ from software hacking?
A4: Hardware hacking focuses on the physical aspects of a device – its circuits, chips, and firmware – while software hacking targets the code, operating systems, and network protocols. Often, the two disciplines intersect when firmware needs to be extracted or manipulated via hardware means.
8. About the Author
This analysis was compiled by The Cha0smagick, a polymath in technology and an elite ethical hacker with extensive experience in digital security and engineering. With a pragmatic and analytical approach, The Cha0smagick transforms complex technical information into actionable blueprints and comprehensive guides, aiming to educate and empower the digital operative community.
9. Mission Debrief: Your Next Steps
Understanding the journey of "Kingpin" is not just about recognizing a legendary figure; it's about internalizing the principles of deep technical curiosity and hands-on exploration that define true engineering and ethical hacking. Joe Grand's life work is a masterclass in deconstruction and understanding.
Your Mission: Execute, Share, and Debate
If this dossier has illuminated the path of hardware hacking for you, consider it your initial operational briefing. The knowledge gained here is a tool, and like any tool, its value is in its application.
Execute: Begin your own exploration. Start with simple devices, methodical analysis, and a commitment to ethical boundaries. Document your findings, just as the legends do.
Share: If this deep dive has provided clarity or saved you significant research time, disseminate this intelligence. Share it within your professional networks. A well-informed operative strengthens the entire community.
Debrief: What aspect of hardware hacking intrigues you most? What challenges have you faced or anticipate facing? What other legendary figures or techniques should we dissect in future dossiers? Your insights are critical for defining our next mission. Engage in the comments below – let's debrief.
Advertencia Ética: La siguiente técnica debe ser utilizada únicamente en entornos controlados y con autorización explícita. Su uso malintencionado es ilegal y puede tener consecuencias legales graves.
For those looking to diversify their understanding and engagement with the evolving digital economy, exploring robust platforms is key. Consider opening an account with Binance to navigate the world of digital assets and related technologies.
Trade on Binance: Sign up for Binance today!